Blogpost
The Q-PrEP Blog
Detailed Information
on Selected Topics of and around PQC
In our blogpost we will give you detailed information on selected topics of and around PQC
- Blogpost # 1: Crypto Agility – The How
- Blogpost # 2: How to Prioritize Systems and Applications for PQC Migration in a Harvest-Now, Decrypt-Later World
- Blogpost # 3: Factors to Consider When Preparing a Budget for PQC Migration
Blogpost # 1: Crypto Agility – The How
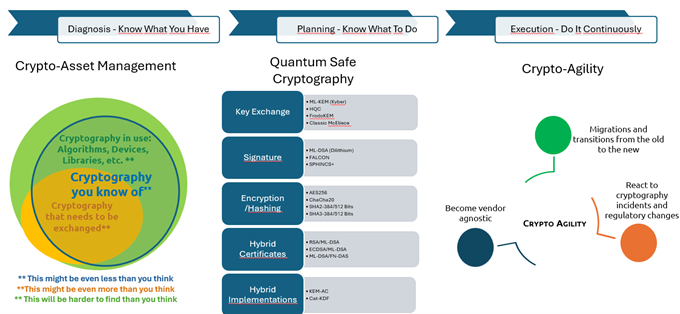
In the era of evolving cyber threats and quantum computing, Crypto Agility (the ability to swiftly switch between cryptographic algorithms and protocols) has become essential. It is no longer just about compliance. It is a strategic advantage that boosts resilience against cyberattacks, quantum risks, and regulatory demands.
This extensive introduction outlines a structured path to Crypto Agility, starting with cryptographic Asset Management: inventorying artefacts using scanning tools and centralized repositories for visibility and control. It emphasizes assessing and tracking cryptographic use, aligning strategy with priorities, and addressing technical and process constraints. Key steps include defining roles, strategic planning, execution, and continuous improvement.
By embedding agility into cryptographic practices, organizations can future-proof infrastructure, maintain resilience, and mitigate emerging threats.
Please read more in our paper on that topic …
Blogpost # 2: How to Prioritize Systems and Applications for PQC Migration in a Harvest-Now, Decrypt-Later World
Summary: In a Harvest-Now, Decrypt-Later (HNDL) scenario, adversaries capture encrypted data today with the aim of decrypting it in the future once quantum computing or other advanced techniques become available.
This poses a serious threat to information requiring long-term confidentiality, such as medical records, intellectual property, and government communications. To stay ahead of this risk, organizations must strategically prioritize the migration of systems and applications to post-quantum cryptography (PQC), considering data sensitivity, business criticality, and complexity of integration.
Developing a clear and actionable migration roadmap is essential to safeguard vital information before quantum threats materialize.
Please read more in our paper on that topic …
Blogpost # 3: Factors to Consider When Preparing a Budget for PQC Migration
Summary: Q-Prep conducted an in-depth interview with Raj Chanian, Post-Quantum Cryptography (PQC) Lead Solutions Architect at Capgemini, to capture expert insights on the financial and operational considerations of PQC migration.
Drawing on his experience, supporting highly regulated organisations, Raj provides a pragmatic, delivery-focused view on how institutions should approach PQC budgeting. His insights emphasise risk-based prioritisation, early discovery, crypto-agility, and alignment with broader modernisation initiatives—helping organisations understand not just what PQC migration costs, but why, when, and how those costs can be effectively managed.

